Without Really Knowing Why They Existed, I Used HTTP, HTTPS, SSL, and TLS for Years
For a long time, these words floated around my career like background noise.
HTTP
HTTPS
SSL
TLS
I used them.
Configured them.
Enabled HTTPS because “security team said so.”
But if someone had asked me early on:
“Why do we actually need all of this?”
“What really happens when you type a URL and hit Enter?”
I would’ve given a half-confident answer and quietly hoped the conversation moved on.
Not because I was careless —
but because everything worked, and that was enough.
Until one day, it wasn’t.
The Moment I Realized I Was Guessing
The real realization didn’t come from a book.
It came from a production issue.
A website was loading… but behaving strangely.
APIs were reachable, but cookies weren’t sticking.
Some users saw warnings. Some didn’t.
Someone asked:
“Is this HTTP or HTTPS?”
“Which TLS version is negotiated?”
“Is the certificate chain correct?”
I nodded.
Then I opened the browser dev tools and realized something uncomfortable:
I had been using the web, not understanding it.
That’s when I decided to slow down and actually follow what happens when a browser hits a website.
It All Starts With a Lie We Tell Ourselves
We often say:
“The browser calls the server.”
That’s not wrong — but it hides a lot.
For content overview videos
https://www.youtube.com/@DotNetFullstackDev
When you type:
https://example.comYou’re not “calling a server”.
You’re triggering a sequence of negotiations, lookups, handshakes, and agreements — most of which happen before any application code runs.
And that’s why HTTP alone was never enough.
Step 1: The Browser Doesn’t Know Where the Website Lives
The first truth:
The browser has no idea where
example.comis.
So the very first thing it does is ask:
“Who knows the IP address for this name?”
That’s a DNS lookup.
No HTTP yet.
No TLS yet.
Just name resolution.
Only after DNS answers does the browser know which machine to talk to.
Step 2: The Browser Opens a Raw Connection
Now the browser has an IP address.
So it opens a TCP connection.
This is still not HTTP.
This is still not HTTPS.
It’s just:
“Hey, I can reach you.”
At this point:
data is unencrypted
identity is unverified
trust is zero
This is where HTTP originally lived.
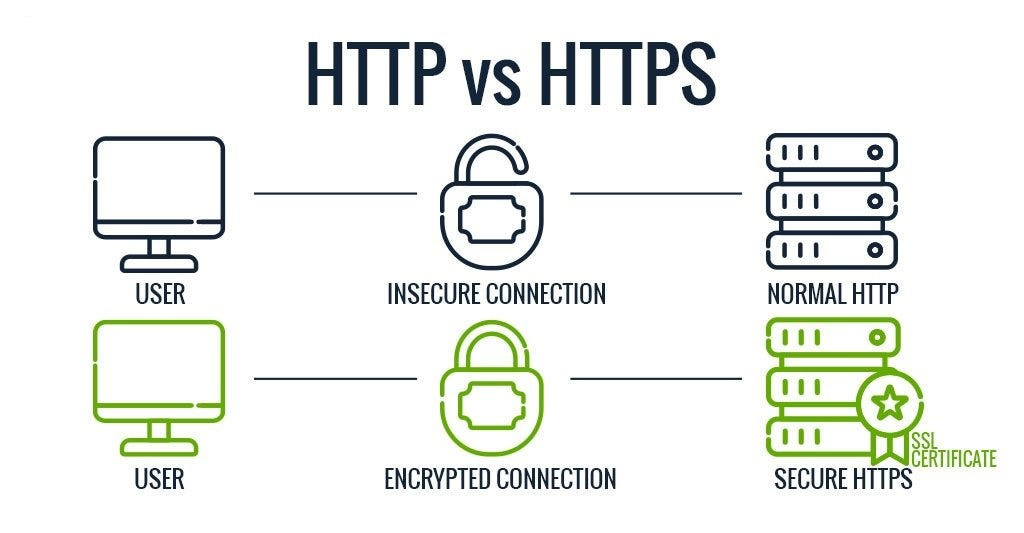
When HTTP Was Enough (And Why It Stopped Being Enough)
Early web days were simple.
HTTP meant:
plain text requests
plain text responses
anyone on the network could read or modify traffic
It worked because:
websites were informational
no logins
no payments
no personal data
But the moment we started sending:
passwords
cookies
tokens
personal data
HTTP became dangerous.
Anyone in between could:
read your credentials
hijack sessions
modify responses
That’s when the web needed something below HTTP.
Enter SSL and TLS (The Invisible Guardians)
Here’s the part that confused me for years:
SSL and TLS are not web technologies.
They don’t know about URLs, controllers, or APIs.
They live below HTTP.
Their job is simple but critical:
“Make this connection private and trustworthy.”
Before a single HTTP request is sent, TLS steps in and asks:
Who are you?
Can I trust you?
Can we talk securely?
How should we encrypt our conversation?
Only if all answers are acceptable does HTTP get a chance to speak.
Step 3: The TLS Handshake (The Real Magic)
This is the moment most people never see.
The browser and server perform a TLS handshake.
Conceptually, this happens:
Browser says: “Here are encryption methods I support”
Server responds: “Here’s my certificate”
Browser verifies:
Is this certificate valid?
Is it issued by a trusted authority?
Does it match the domain?
Is it expired or revoked?
If anything fails — everything stops.
No HTTP request.
No controller.
No API.
This is why HTTPS failures feel so dramatic.
Why Certificates Exist (And Why They Matter)
Certificates solve one critical problem:
How do you know the server you’re talking to is who it claims to be?
Without certificates:
anyone could pretend to be
example.comencryption alone wouldn’t help
you’d encrypt data… to the wrong person
Certificates tie:
domain name
public key
trusted authority
This is how browsers build trust without knowing your server personally.
Step 4: HTTPS Is Just HTTP With Armor
Here’s the big realization that clicked for me:
HTTPS is not a different protocol.
It’s HTTP inside a secure tunnel.
Once TLS finishes:
HTTP requests are sent normally
headers, cookies, payloads behave the same
your application code sees no difference
The difference is:
nobody else can read it
nobody can alter it
the server identity is verified
That’s it.
HTTPS doesn’t change how you write APIs.
It changes who can see and trust them.
Keep the Momentum Going — Support the Journey
If this post helped you level up or added value to your day, feel free to fuel the next one — Buy Me a Coffee powers deeper breakdowns, real-world examples, and crisp technical storytelling.
Where Cookies, Sessions, and Auth Depend on This
This is where everything connects.
Cookies only work securely because:
HTTPS protects them from being stolen
TLS prevents session hijacking
browsers enforce secure cookie rules
Without HTTPS:
authentication falls apart
sessions become vulnerable
trust collapses
That’s why modern browsers now block sensitive features on HTTP.
Security moved from “nice to have” to “non-negotiable”.
Step 5: The Actual HTTP Request Finally Happens
Only now does the browser send:
GET / HTTP/1.1
Host: example.com
At this point:
the connection is encrypted
the server is trusted
cookies are attached
headers are intact
Your server code finally runs.
Controllers execute.
Middleware triggers.
Responses are generated.
But all of this sits on top of what already happened.
Why We Need All of This (The Simple Truth)
Each layer exists because the one above it assumes safety.
HTTP assumes a reliable connection
HTTPS assumes a trusted identity
Cookies assume encryption
Authentication assumes integrity
Remove one layer, and the rest become fragile.
This isn’t complexity for the sake of it.
It’s defense built from experience.
The Moment It Finally Made Sense to Me
The day this truly clicked was when I realized:
Application security doesn’t start in your code.
It starts before your code even runs.
HTTP, HTTPS, TLS, certificates —
they’re not optional add-ons.
They’re the foundation that makes modern applications possible.
Final Thought
👉 I’ve shared the JWT Authentication Boilerplate for ASP.NET Core (.NET 8)
(Instant download, production-ready, no fluff)
Next time you type a URL and hit Enter, remember:
You’re not “opening a website”.
You’re:
resolving identity
negotiating trust
agreeing on encryption
establishing privacy
and only then… exchanging data
All in a fraction of a second.
Once you see that,
words like HTTP, HTTPS, SSL, and TLS stop being confusing acronyms.
They become quiet guardians — doing their job so your application code can do its own.
And when you understand that, you stop taking the web for granted.
You start respecting it.